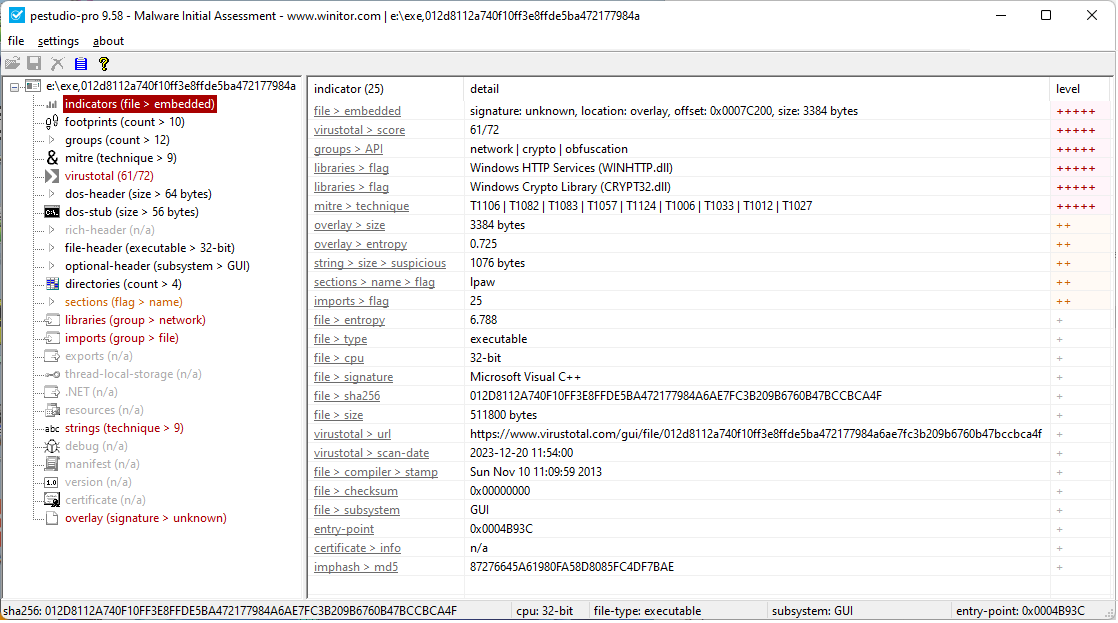
Malware Initial Assessment
Accelerate your malware assessment workflow by quickly identifying key indicators of Windows executable files.
Since its inception in 2009, pestudio has been continuously enhanced to meet evolving requirements. Therefore, pestudio is trusted by Computer Emergency Response Teams (CERT), Security Operations Centers (SOC), and Digital Forensic Incident Response (DFIR) professionals around the world.
Following document highlights the main features of pestudio.